Recently reported (first by motherboard) all this week, Taiwanese tech-giant ASUS has fallen victim to a supply chain hack (or attack). My reasoning for calling this a “hack” is due to how the update server compromised in this attack was utilised. Much like previous supply chain hacks (notably the CCleaner mess) the scope of affected machines is huge (roughly half a mil currently).
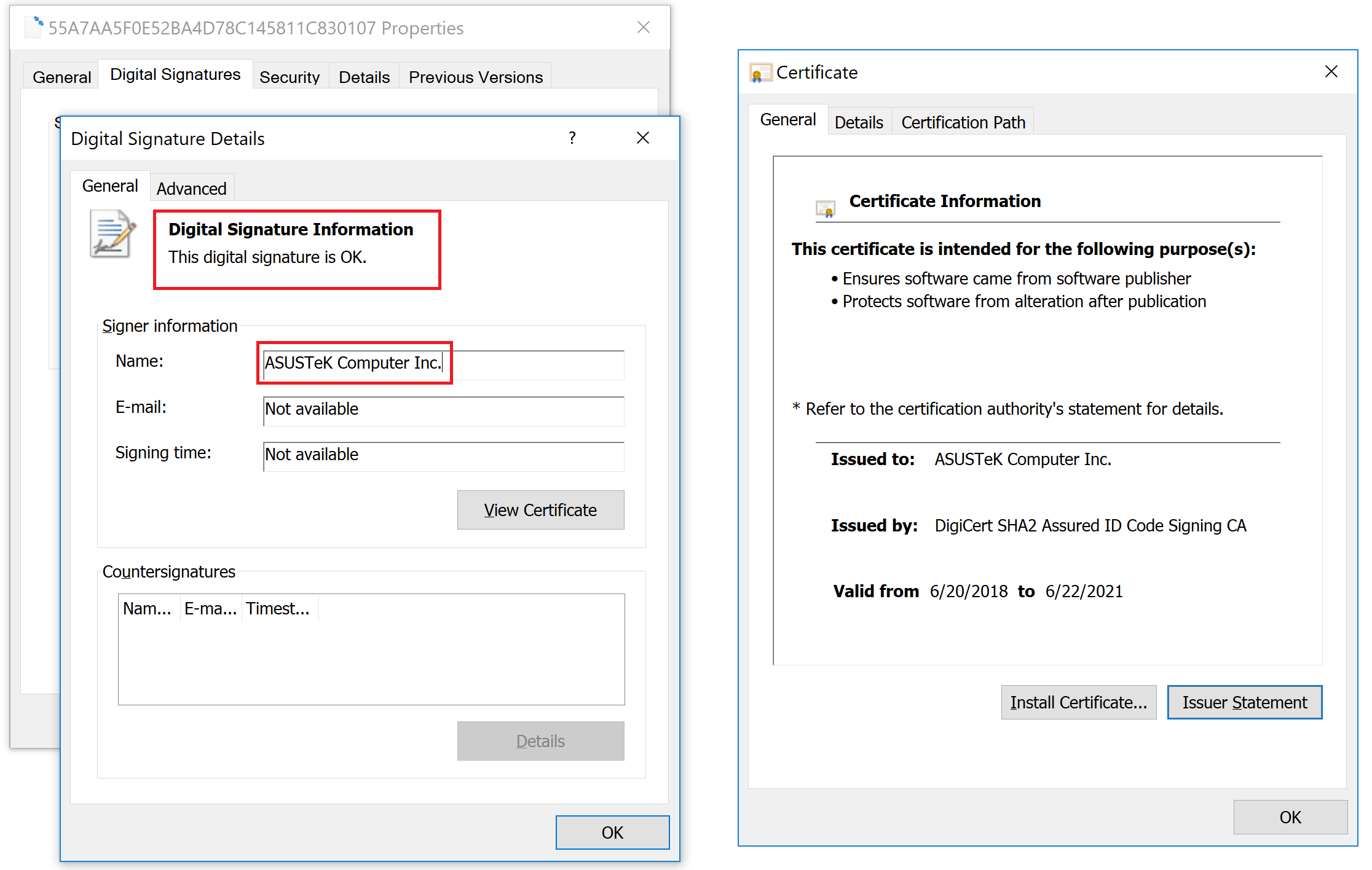
The difference in this Hack from opportunist intrusion is the level of sophistication taken at almost every step. The below is taken from Kaspersky’s initial report on the hack (as their software detected it on over 50k machines worldwide):
“The trojanized utility was signed with a legitimate certificate and was hosted on the official ASUS server dedicated to updates, and that allowed it to stay undetected for a long time. The criminals even made sure the file size of the malicious utility stayed the same as that of the original one.”
Kaspersky reporting on shadowhammer
This is only a part of the story, as though the malware/spyware had the capability to infect many devices, it was only hard encoded to attempt to compromise devices with a corresponding MAC address. Kaspersky reported further stating:
“According to our statistics, more than 57,000 users of Kaspersky Lab’s products have installed the backdoored utility, but we estimate it was distributed to about 1 million people total. The cybercriminals behind it were not interested in all of them, however — they targeted only 600 specific MAC addresses, for which the hashes were hardcoded into different versions of the utility.”
Check your MAC address with Kaspersky’s tool found here
ASUS gave their official statement and provided a tool to check if your system was affected, however Kaspersky have also released a tool to check if your machine was one of the 600+ MAC addresses hard encoded into the malware to be infected. With ASUS admitting themselves that this was the act of an APT group (state sponsored actors/hackers) there is a high chance there is far more behind this attack then just sophisticated intrusion.
There are conclusions being drawn that this actor is the same as similar other APT cases (specifically the BARIUM actors in the Shadowpad hacking cases) are the same (or share the same tools) as some spotted already.
My personal assumptions is that an attack of this scale requires either insider knowledge or a strong (and unchecked) foothold into not just their networks, but into an understanding of their processes/server locations and access to their signed certificates. If you are using an ASUS machine, do check the tools posted earlier in this article and use the below FAQ to ensure you have the latest ASUS update utility (or just get rid of their bloatware all together).
UPDATE 28-3-19
The security firm Skylight has brute forced the MAC addresses contained within the Kaspersky checking tool to assist enterprises that have a mass number of machines to check. Their post details how they used a combination of Hashcat (cracking tool) and an Amazon Web Server (AWS) in order to decipher 583 of the 619 targeted MAC addresses. The plain text list is here. The reasoning and stance skylight has on this is outlined in their post:
“First thing’s first – if information regarding targets exists, it should be made publicly available to the security community so we can better protect ourselves.
Skylight state their reason for releasing the list of affected MAC addresses, which I can see arguments on both sides for.
Kaspersky have released an online tool that allows you to check your MAC address against a DB of victim MAC addresses (which is hidden).
Good on Kaspersky on one hand, but on the other hand, this is highly inefficient, and does not really serve the security community.”