
Earlier today Elena Root & Andrey Polkovnichenko of Checkpoint released this report indicating that over 150 million android devices have been infected via multiple legitimate games found in the Google play store.
A variety of legitimate mobile games downloaded millions of times (and created by different developers) have been infected due to a malicious SDK. An SDK (software development kit) are packages used by developers to either provide functionality, access to advertising networks or add specific features in their software/apps. The checkpoint report states:
Taken from the checkpoint report a nasty consequence of not checking supply chains/vendors.
“Inside the SDK
The malware resides within the ‘RXDrioder’ Software Development Kit (SDK), which is provided by ‘addroider[.]com’ as an ad-related SDK. We believe the developers were scammed to use this malicious SDK, unaware of its content, leading to the fact that this campaign was not targeting a specific county or developed by the same developer. The malware has been dubbed ‘SimBad’ due to the fact that a large portion of the infected applications are simulator games. “
The report goes onto state it’s current capabilities and what it has been harnessed to do. It basically is generating revenue for the original makers by making ad-traffic through millions of devices. The Adware is resilient and carries out various functions to not only make it self hard to remove, but providing itself more power over the device (enough to publish ads during normal phone usage). This is explained below in the report:
“What Does SimBad Do?
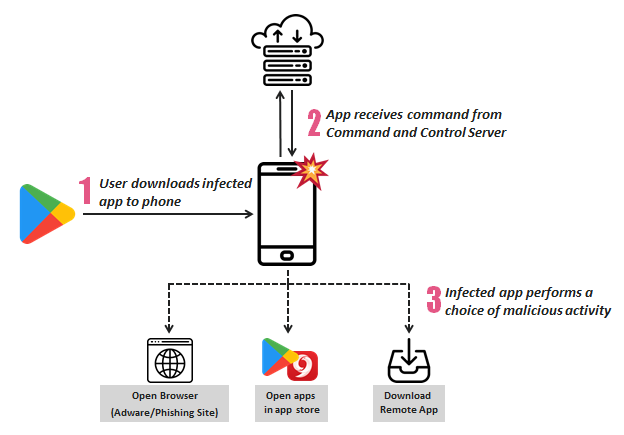
‘SimBad’ has capabilities that can be divided into three groups – Show Ads, Phishing, and Exposure to other applications. With the capability to open a given URL in a browser, the actor behind ‘SimBad’ can generate phishing pages for multiple platforms and open them in a browser, thus performing spear-phishing attacks on the user.
With the capability to open market applications, such as Google Play and 9Apps, with a specific keyword search or even a single application’s page, the actor can gain exposure for other threat actors and increase his profits. The actor can even take his malicious activities to the next level by installing a remote application from a designated server, thus allowing him to install new malware once it is required.”
The capabilities and current functions of SimBad explained
Google has currently removed the offending games but this has highlighted there are still flaws in the security mechanisms and AI made to check for malware/infections across all the apps in the playstore. Similar adware campaigns were spotted just last year.
The report goes indepth with information regarding the C&C (command and control) servers and domain used in this campaign. Interestingly, though whois information is set to private and registered with Godaddy the A records where this points to (amazon web servers) have remained fairly unchanged for almost a year. I found this when checking myself: https://securitytrails.com/domain/addroider.com/history/a

The checkpoint researchers make the conclusion that the domain was most likely parked after expiring 7 months ago, but the history of A Records and the server IP addresses (with them ALL being amazon web servers) make me believe that this was an attack in the making (rather than a grab of oppertunity on a valuable domain).
There is one highlighted point that I must agree with however, the infrastructure and power this type of infection has over a device can be utilised for far more malicious purposes than just advertising. As this framework allows the “controllers” or malicious actors to launch URL’s at will on an infected device, this alone leaves an endless possibility of malicious use and more dangerous impacts (botnet anyone?).
This is another prime example of why all third party vendors or supply chains require their own testing/checking. SDK’s need to be analysed before being willingly used by developers to ensure their end users are not downloading packaged malware due to their lack of sanity checks.
I’d like to finish this off to say thanks again for the research carried out by Elena & Andrey and the means of disclosure. This story deserves all the recognition it gets and I especially appreciate the researchers giving their own take on what they found.